Threat Intelligence Software
See threats early. Act with confidence.
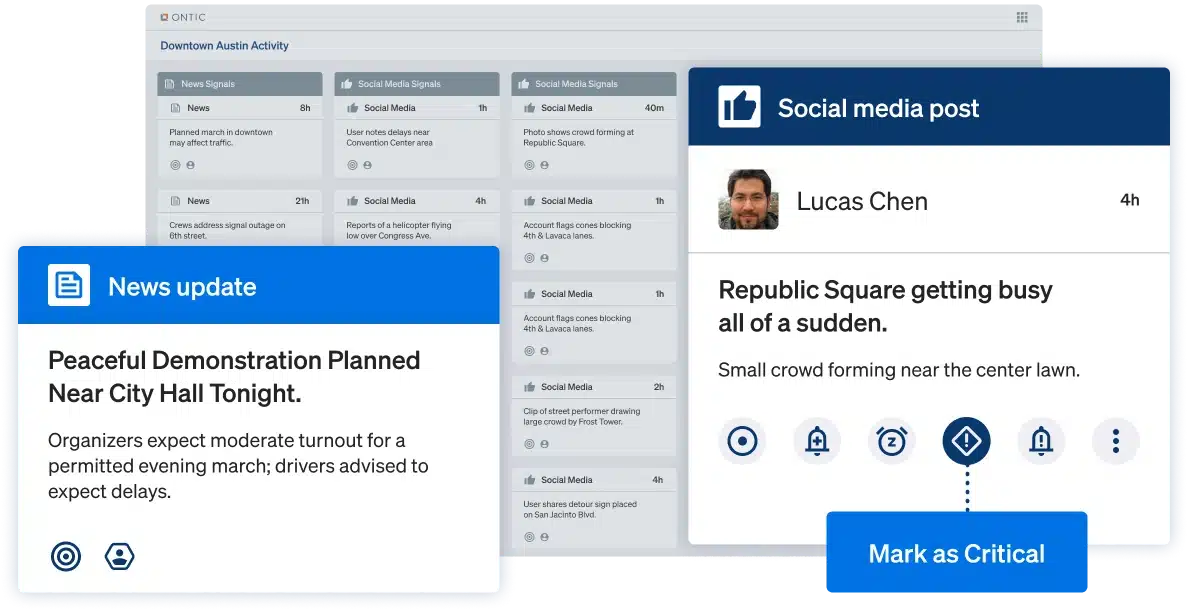
Ontic cuts through digital noise to surface credible, relevant signals. Monitor the right sources, identify who’s behind concerning posts, and know if they’re a real risk — all in one unified platform.
Proven threat management outcomes by the numbers
Based on verified outcomes from Ontic clients — including Fortune 100 security teams.
2x more
credible signals identified
Faster
signal to assessment time
50%
faster risk assessments
How it Works
Connected Intelligence for faster, smarter action
Disconnected feeds force analysts to chase context, manually stitch together information, and risk missing real threats. Ontic unifies your threat intelligence — linking external signals to your people, assets, and locations — so your team sees the full picture, responds quickly, and mitigates real-world risk.
The Solution
How Ontic transforms reactive operations into proactive, connected security
Ditch siloed threat intelligence software for one connected platform that unifies detection, investigation, and response — so you get ahead of threats and stay aligned on action.
Better Outcomes
Intelligence that leads to action
Find threats faster
Cut through the noise to surface credible signals tied to your people, places, and operations.
Investigate with confidence
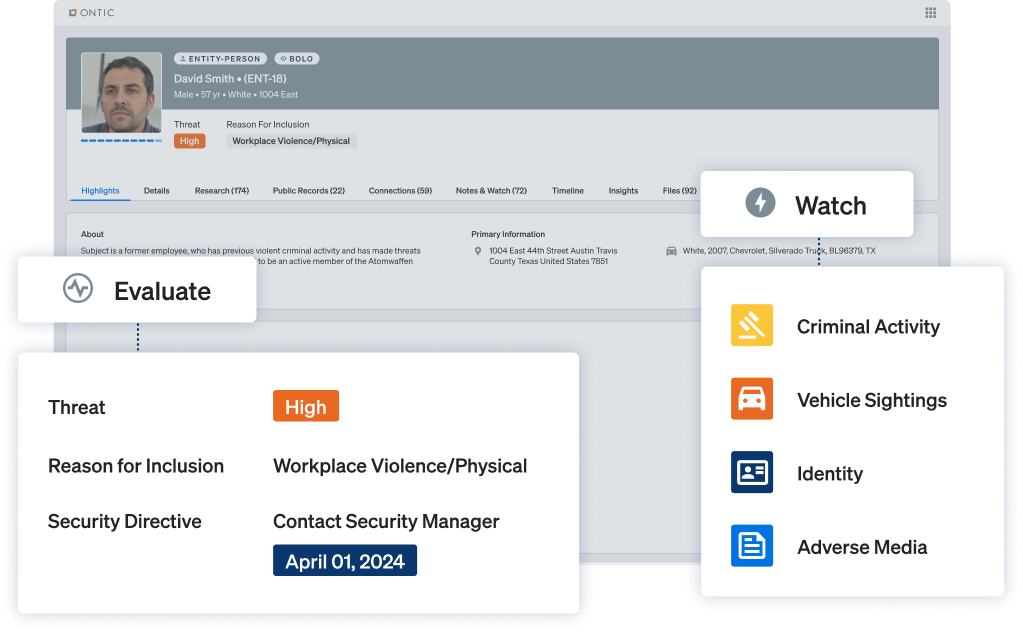
Quickly understand who’s behind a signal and whether it’s worth your team’s time.
Deliver trusted intelligence
Move from collection to briefing with contextual, verified insights your leadership trusts.
Featured Products
Built for real-world threats.
Tailored for physical security.
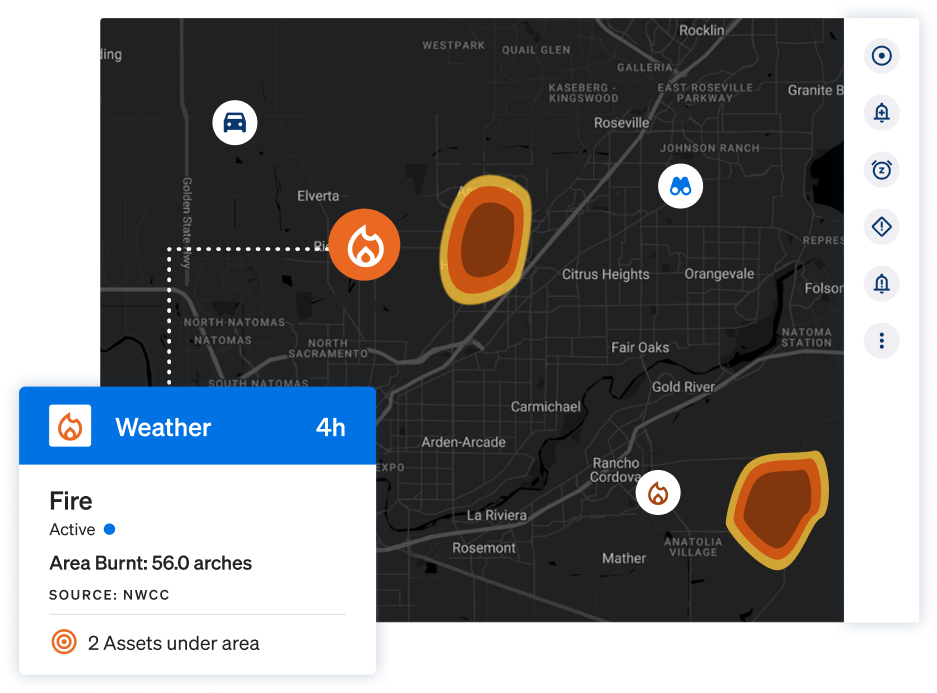
Risk Intelligence
- Targeted OSINT Monitoring
- Social Media
- Dark Web
- Fringe Platforms
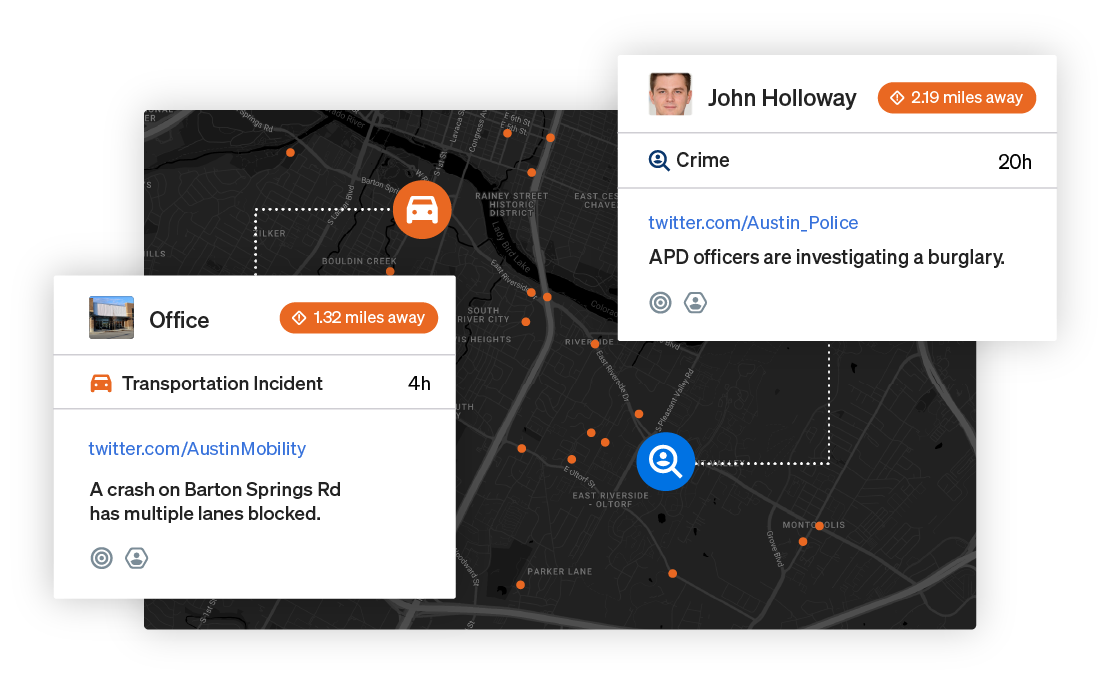
- Geo-based Risk Events
- Weather and Crime
- Analyst-Verified Intelligence
Multi-sourced threat signals, intelligence, and 24/7 monitoring for early detection, analysis, and response.
Integrated Research
- Identity Resolution
- Digital Footprint
- Vehicle Sightings
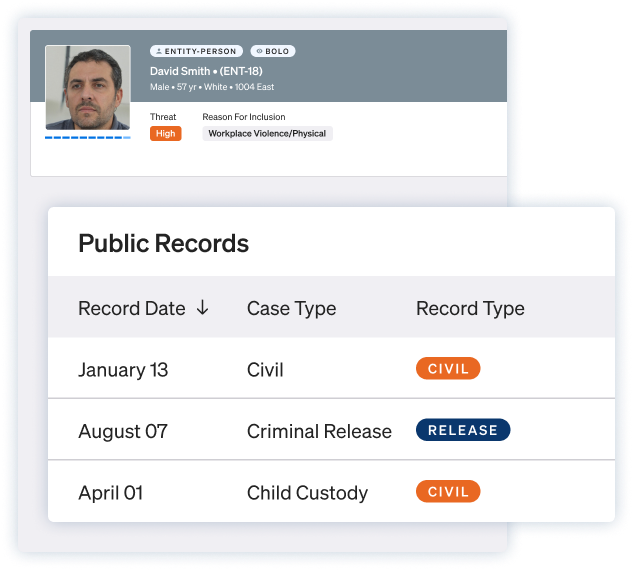
- Public Records
- TLOxp
Comprehensive investigative research and monitoring tools integrated directly into your case workflow.
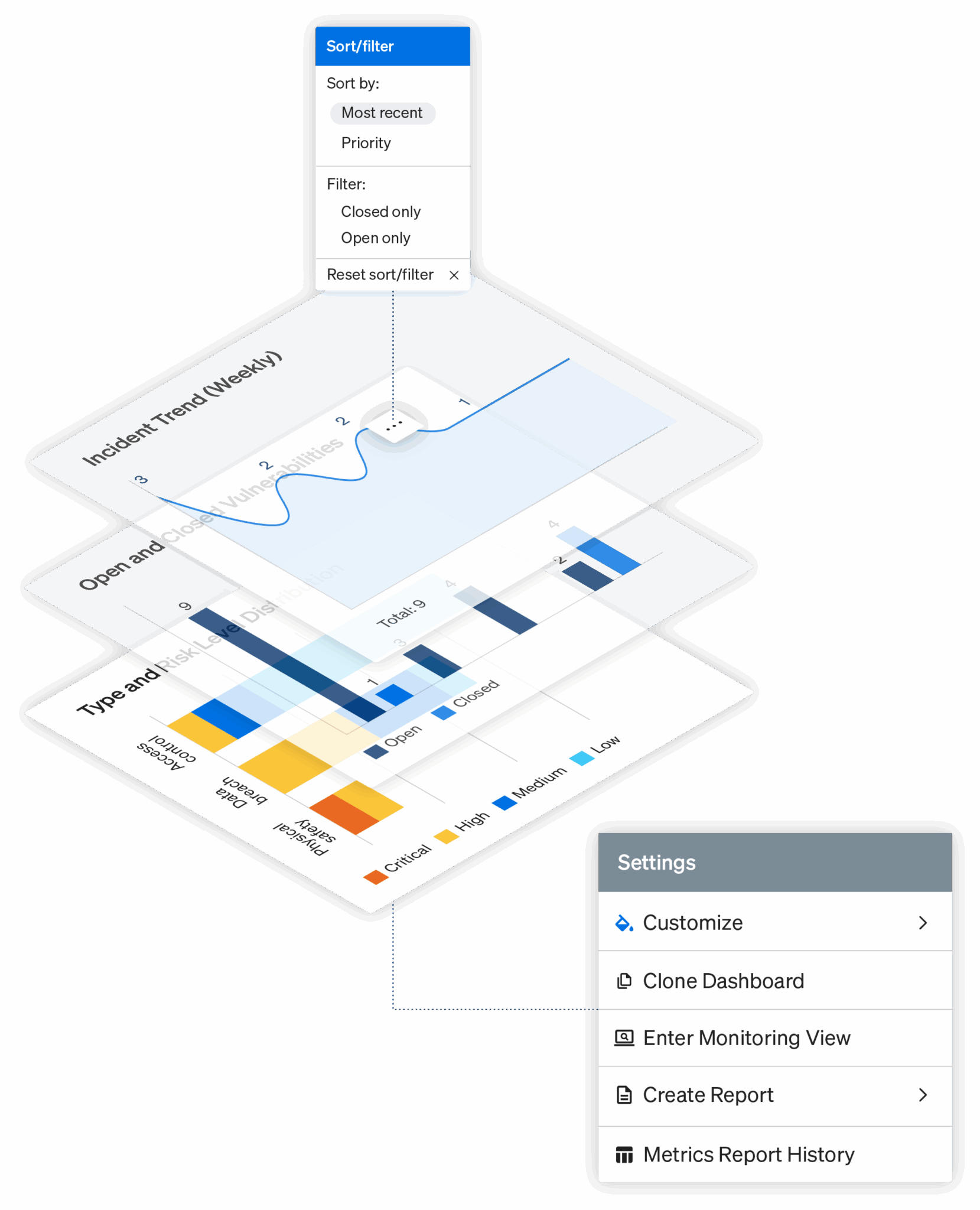
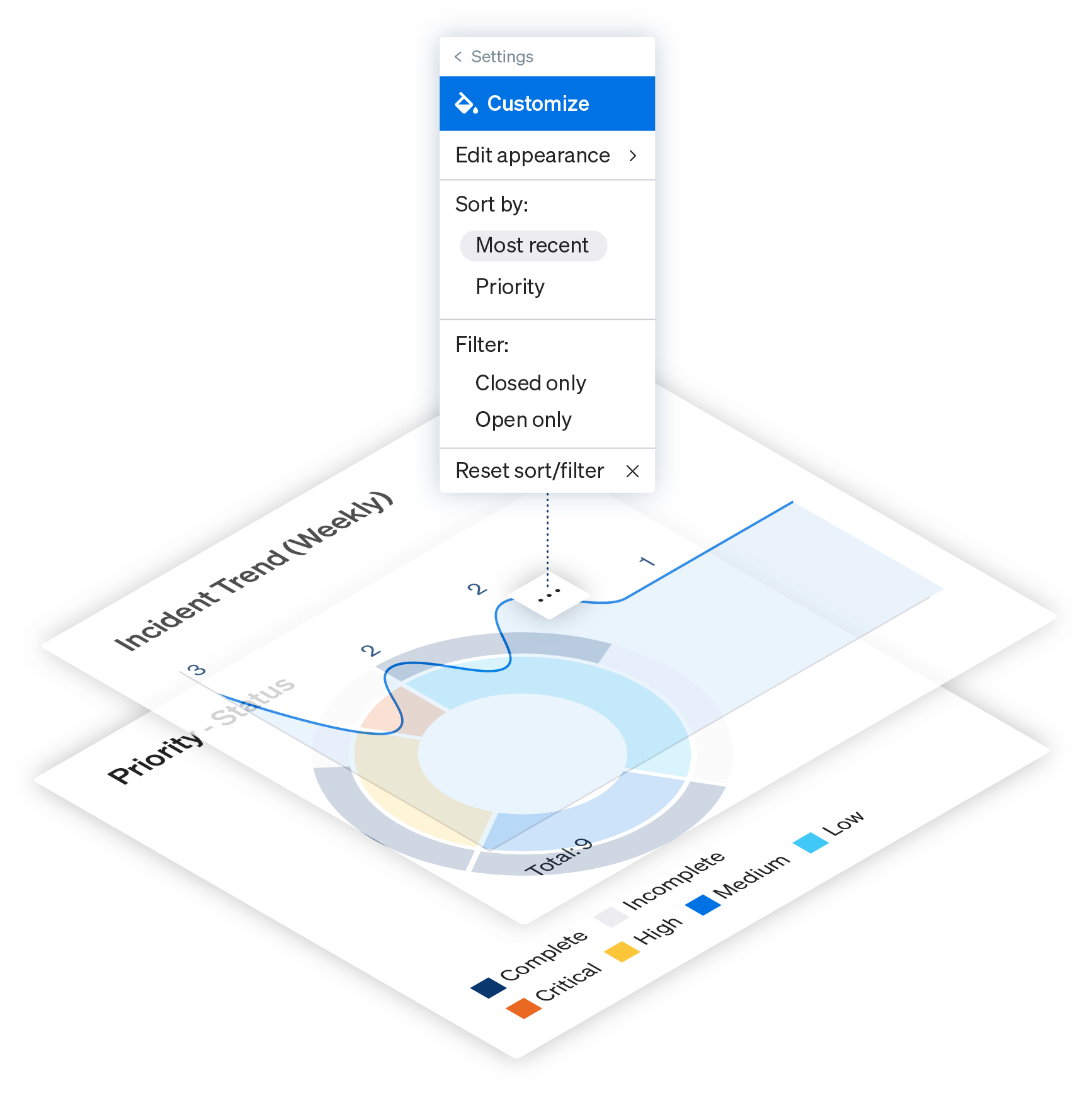
Core Platform
- Central Data Management
- Workflow Automation
- Maps and Visualizations
- Metrics and Reporting
- Role-based Access Controls
Govern your entire security operation from one secure platform – centralize data, automate workflows, and configure access controls for secure, efficient team collaboration.