Building Topics in Ontic: Best Practices
Ontic Connect Boston
Boston is increasingly a focal point for coordinated activism and geopolitical discourse. Major global events, geopolitical disruptions, and periods of heightened visibility increasingly force executive protection, investigations, intelligence, and operations programs to engage all at once—often without shared context or clear decision-making. Employee activism and public protests are now frequent catalysts for these moments, accelerating…
Read MoreThank You for Registering for Ontic Connect Boston!
Ontic Connect San Francisco
Major global events, geopolitical disruptions, and periods of heightened visibility increasingly force executive protection, investigations, intelligence, and operations programs to engage all at once, often without shared context or clear decision-making. These moments demand faster communication, clearer escalation, and tighter coordination across security, HR, cyber, legal, communications, and executive leadership. This session is built for…
Read MoreThank You for Registering for Ontic Connect San Francisco!
How Activism and Executive Risk Converge Today
A new era of executive protection demands an intelligence-driven, socially aware approach that goes far beyond bodyguards By Cynthia Marble and Rachel Briggs This article was originally posted in ASIS Security Management. In December 2024, the corporate security community was shaken by the murder of UnitedHealthcare CEO Brian Thompson. The response in some corners of…
Read MoreWhat to do When Your Executive or Company Takes a Public Stance — or Chooses Silence
What to do When Your Executive or Company Takes a Public Stance — or Chooses Silence
With the steps outlined in this checklist, you will:
Read MoreBuilding NITTF-Aligned Insider Risk Programs for Government Organizations
Building NITTF-Aligned Insider Risk Programs for Government Organizations
With this assessment, you can:
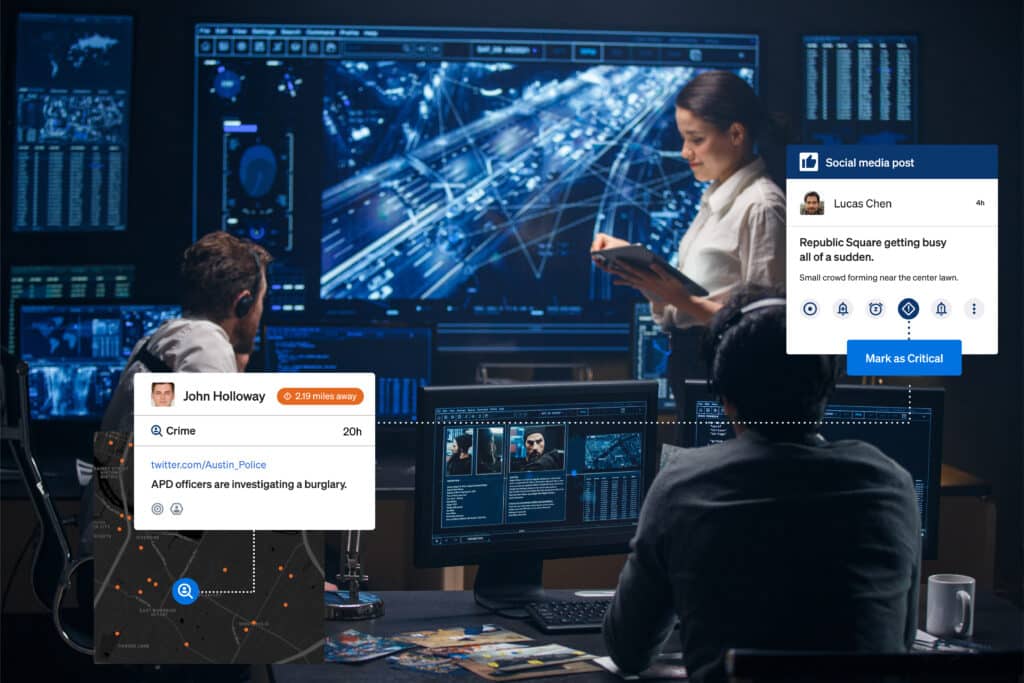
Read MoreHow Federal Agencies Can Connect Digital Intelligence to Real-World Action
Bringing digital intelligence and ground-level protective measures into a unified approach For decades, hardened perimeters, controlled access points, and well-rehearsed protective operations have formed the backbone of federal security. Those measures remain essential. But today’s most consequential threats rarely originate at a checkpoint. They begin online. Across social networks, fringe forums, dark web channels, and…
Read MorePositioning Security as a Business Enabler: Strategies for Success with Jeremy Baumann
In this episode Host Fred Burton sits down with Jeremy Baumann, CEO and founder of Corporate Security Advisors, to explore what it truly means to build high-performing, business-aligned security programs. Drawing on three decades of experience across law enforcement, corporate security, and consulting, Jeremy shares how security leaders can move beyond being seen as a…
Read MoreSecuring the Spotlight: Inside the Investigations That Protect America’s Largest Events
Security starts from within. The most sophisticated perimeter protection and threat detection systems cannot compensate for insider risk that goes unexamined. This article was originally posted in Federal News Network. At large-scale events like World Cup matches, a Super Bowl or the LA 2028 Olympics, viewers around the world will turn their attention to the…
Read MoreThe Evolution of Aviation Security: Managing Risk at a Global Scale with Rich Davis
In this episode In this episode, Fred Burton sits down with Rich Davis, former Chief Security Officer of United Airlines, to explore the evolution of aviation security and what it takes to manage risk at a truly global scale. Drawing on decades of leadership experience, Rich shares how collaboration, intelligence sharing, and a strong duty…
Read More